Simplify your Cloud Run security with Identity Aware Proxy (IAP)
Cloud Run provides a powerful and scalable platform for deploying applications. Today, we’re introducing the general availability of two major enhancements to Cloud Run security: direct Identity-Aware Proxy (IAP) integration, and a way to allow public access to Cloud Run services that is compatible with Domain Restricted Sharing (DRS).
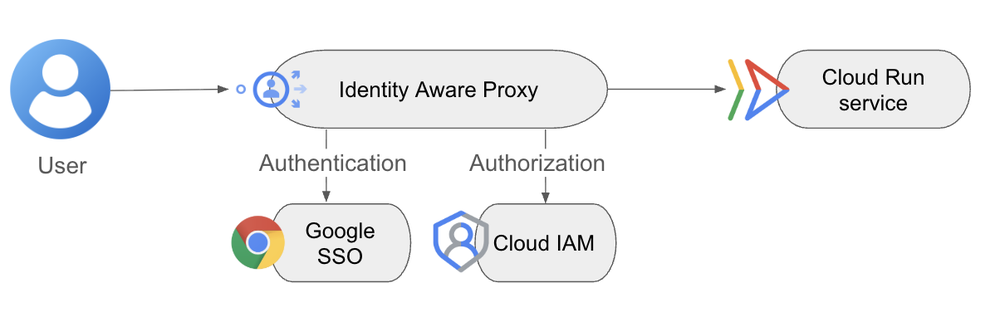
Introducing direct IAP on Cloud Run
IAP lets you easily control user access to applications running in Google Cloud. Integrating IAP with Cloud Run previously required you to manually configure application load balancers and other complex network settings. This added operational overhead detracted from Cloud Run's core promise of serverless simplicity.
That changes today! You can now enable IAP directly on Cloud Run in a single click, with no load balancers, and at no added cost. Google Cloud does not charge for IAP (with some exceptions), and it incurs no load balancer costs.
Enable IAP authentication directly on a Cloud Run service
Why this matters:
*
Simplified enablement: Turn on IAP in the UI or with a single flag (--iap) through gcloud, significantly simplifying deployments and saving valuable time and effort.
*
Enterprise-grade security for all web apps: Use IAP’s authentication and authorization policies based on user or group identities, as well as context-aware factors like IP address, geolocation, and device security status.
*
Support for Workforce Identity Federation: Easily manage access for your employees and partners using your existing identity providers.
*
Simplified Cross-Origin Resource Sharing (CORS): Configure IAP directly on Cloud Run to allow unauthenticated HTTP OPTIONS for CORS requests. This helps satisfy browser preflight checks while ensuring all other requests undergo authentication.
We are already seeing a big uptake in organizations adopting IAP to secure Cloud Run workloads, for example, at L’Oreal.
“L'Oréal relies on Google Cloud's Identity-Aware Proxy (IAP) as a critical layer of security, ensuring that access to every web application we host on Google Cloud is meticulously filtered and controlled. The beauty of IAP lies in its simplicity and effectiveness; it's a self-managed solution that's not only free but also exceptionally straightforward to implement across our diverse application landscape. This ease of deployment, combined with a security posture that surpasses what we could achieve with custom-built solutions, makes IAP an indispensable tool for protecting our digital assets.” - Antoine Castex, Group Data & A.I Architect, L'Oréal
Allow public access when using DRS
New simplified Cloud Run authentication UI
While IAP is the recommended authentication mechanism for internal business applications on Cloud Run, Cloud IAM remains essential for managing service-to-service communication.
Historically, Cloud Run's default behavior was to perform an IAM check (run.invoker role) on every request to an HTTPS endpoint. While this provided a strong security baseline, it had the potential to become a bottleneck when the intent was to create public apps, particularly when organizations also enforced the Domain Restricted Sharing policy.
You can now disable this IAM "invoker" check by selecting “Allow Public access” for your applications.
This gives you flexibility to rely on other security layers like organization policies, network-level controls, or custom authn/authz for your services. It also unlocks broader use cases:
* Public websites: Host a store locator site on Cloud Run and make it accessible to everyone — even if your Org Policy restricts sharing (DRS enabled). You can do this by selecting “Allow Public access” and setting ingress to ‘All’.
*
Private microservices: For services behind an internal ingress where network-level security is sufficient, you can bypass the IAM check by selecting “Allow Public access”.
“Bilt Rewards leverages the 'disable IAM' feature for multiple mission-critical Cloud Run services deployed in multi-regional topologies. By disabling IAM on these instances, we establish a direct, unimpeded path from our edge, while maintaining security using Cloud Armor on the global load balancer. This simplified approach reduces infrastructure complexity and provides a more performant solution while maintaining org-wide security posture through organizational policies.” - Kosta Krauth, CTO Bilt Rewards
Getting started
Ready to get started? You can easily enable IAP directly on Cloud Run.
Learn more:
*
IAM in Cloud Run
*
Ingress settings
*
Domain-restricted sharing 🔗 Google Security
https://cloud.google.com/blog/products/serverless/iap-integration-with-cloud-run/?utm_source=dlvr.it&utm_medium=blogger
Introducing direct IAP on Cloud Run
IAP lets you easily control user access to applications running in Google Cloud. Integrating IAP with Cloud Run previously required you to manually configure application load balancers and other complex network settings. This added operational overhead detracted from Cloud Run's core promise of serverless simplicity.
That changes today! You can now enable IAP directly on Cloud Run in a single click, with no load balancers, and at no added cost. Google Cloud does not charge for IAP (with some exceptions), and it incurs no load balancer costs.
Enable IAP authentication directly on a Cloud Run service
Why this matters:
*
Simplified enablement: Turn on IAP in the UI or with a single flag (--iap) through gcloud, significantly simplifying deployments and saving valuable time and effort.
*
Enterprise-grade security for all web apps: Use IAP’s authentication and authorization policies based on user or group identities, as well as context-aware factors like IP address, geolocation, and device security status.
*
Support for Workforce Identity Federation: Easily manage access for your employees and partners using your existing identity providers.
*
Simplified Cross-Origin Resource Sharing (CORS): Configure IAP directly on Cloud Run to allow unauthenticated HTTP OPTIONS for CORS requests. This helps satisfy browser preflight checks while ensuring all other requests undergo authentication.
We are already seeing a big uptake in organizations adopting IAP to secure Cloud Run workloads, for example, at L’Oreal.
“L'Oréal relies on Google Cloud's Identity-Aware Proxy (IAP) as a critical layer of security, ensuring that access to every web application we host on Google Cloud is meticulously filtered and controlled. The beauty of IAP lies in its simplicity and effectiveness; it's a self-managed solution that's not only free but also exceptionally straightforward to implement across our diverse application landscape. This ease of deployment, combined with a security posture that surpasses what we could achieve with custom-built solutions, makes IAP an indispensable tool for protecting our digital assets.” - Antoine Castex, Group Data & A.I Architect, L'Oréal
Allow public access when using DRS
New simplified Cloud Run authentication UI
While IAP is the recommended authentication mechanism for internal business applications on Cloud Run, Cloud IAM remains essential for managing service-to-service communication.
Historically, Cloud Run's default behavior was to perform an IAM check (run.invoker role) on every request to an HTTPS endpoint. While this provided a strong security baseline, it had the potential to become a bottleneck when the intent was to create public apps, particularly when organizations also enforced the Domain Restricted Sharing policy.
You can now disable this IAM "invoker" check by selecting “Allow Public access” for your applications.
This gives you flexibility to rely on other security layers like organization policies, network-level controls, or custom authn/authz for your services. It also unlocks broader use cases:
* Public websites: Host a store locator site on Cloud Run and make it accessible to everyone — even if your Org Policy restricts sharing (DRS enabled). You can do this by selecting “Allow Public access” and setting ingress to ‘All’.
*
Private microservices: For services behind an internal ingress where network-level security is sufficient, you can bypass the IAM check by selecting “Allow Public access”.
“Bilt Rewards leverages the 'disable IAM' feature for multiple mission-critical Cloud Run services deployed in multi-regional topologies. By disabling IAM on these instances, we establish a direct, unimpeded path from our edge, while maintaining security using Cloud Armor on the global load balancer. This simplified approach reduces infrastructure complexity and provides a more performant solution while maintaining org-wide security posture through organizational policies.” - Kosta Krauth, CTO Bilt Rewards
Getting started
Ready to get started? You can easily enable IAP directly on Cloud Run.
Learn more:
*
IAM in Cloud Run
*
Ingress settings
*
Domain-restricted sharing 🔗 Google Security
https://cloud.google.com/blog/products/serverless/iap-integration-with-cloud-run/?utm_source=dlvr.it&utm_medium=blogger