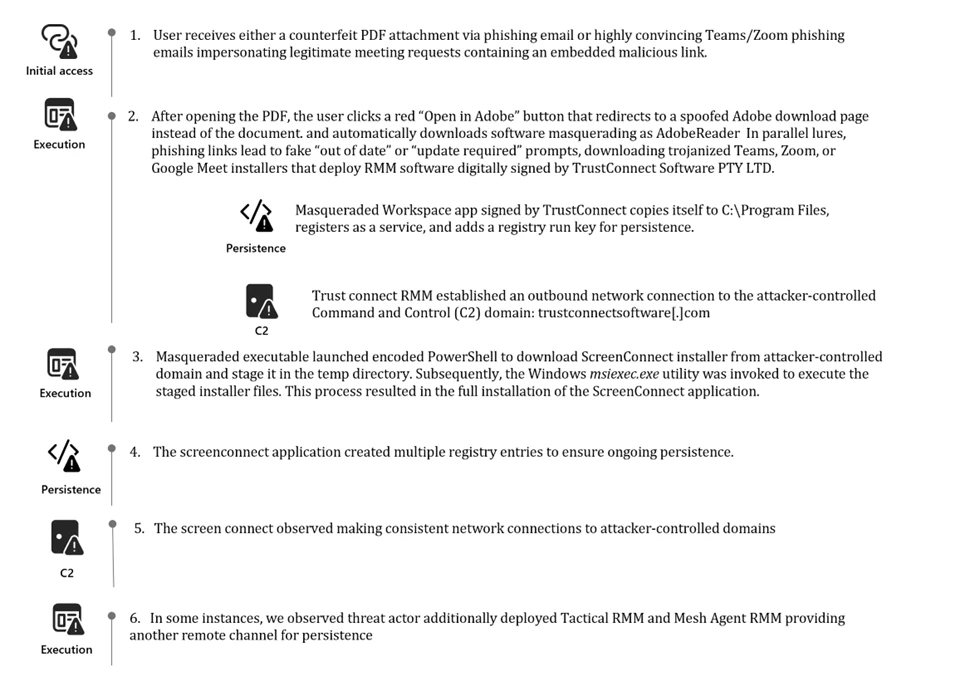
Signed malware impersonating workplace apps deploys RMM backdoors
Signed malware backed by a stolen EV certificate deployed legitimate RMM tools to gain persistent access inside enterprise environments. Organizations must harden certificate controls and monitor RMM activity to reduce exposure.
The post Signed malware impersonating workplace apps deploys RMM backdoors appeared first on Microsoft Security Blog. 🔗 MS Infosec
https://www.microsoft.com/en-us/security/blog/2026/03/03/signed-malware-impersonating-workplace-apps-deploys-rmm-backdoors/?utm_source=dlvr.it&utm_medium=blogger
The post Signed malware impersonating workplace apps deploys RMM backdoors appeared first on Microsoft Security Blog. 🔗 MS Infosec
https://www.microsoft.com/en-us/security/blog/2026/03/03/signed-malware-impersonating-workplace-apps-deploys-rmm-backdoors/?utm_source=dlvr.it&utm_medium=blogger